Filters
 09:47
09:47
2025 in Review: Anyone Can Be Labeled a Spy
A review of 2025 for the human rights project Perviy Otdel (“First Department”) and for...
2 months ago 12:56
12:56
Donate Safely! How Security Forces Track Crypto
Recently, the FSB announced that it had detained a Russian accused of treason for transferring...
2 months ago 11:36
11:36
Sovereign digital certificates. What is it and why?
Russian banks have begun to demand digital certificates from the Ministry of Digital Development, without...
2 months ago 20:14
20:14
Telegram meta-universe. How law enforcement agencies find you
Since Pavel Durov's arrest in Paris, Russian and foreign media have published numerous articles about...
2 months ago 19:22
19:22
The all-seeing eye? How surveillance and facial recognition works
In Moscow, surveillance cameras with a facial recognition system are widely used, actively used for...
2 months ago 13:59
13:59
We're being watched: How SORM works
There is a lot of information of varying degrees of reliability available on the Internet...
2 months ago 10:05
10:05
Big Brother. History of surveillance
Holmes versus Moriarty. Bastrykin versus a magnifying glass. Aristotle versus a press with spikes. The...
2 months ago 35:21
35:21
How Russia’s FSB Is Structured
The FSB is a massive structure made up of dozens of divisions. Thousands of officers...
2 months ago 11:25
11:25
FSB-taxi: special services will trace your every trip
The FSB will be able to monitor your every taxi ride. According to the new...
2 months ago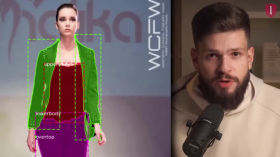 18:29
18:29
How Digital Racism Works
AI is increasingly being used for racial segregation and political control — from “smart” surveillance...
2 months ago 11:22
11:22
Does Telegram Work with the FSB?
An investigation into Telegram’s possible ties to the FSB sparked strong reactions and widespread suspicion,...
2 months ago 12:10
12:10
Cryptography. Debunking the myth of omnipotent intelligence services
"There's no point in defending yourself, the FSB has access to everything anyway" - these...
2 months ago 00:50
00:50
How you can be wiretapped
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 01:58:13
01:58:13
Mikhail Klimarev’s Lecture: “The History of Digital Resistance in Runet”
Mikhail Klimarev speaks at Reforum Space Berlin about how pressure from Russian authorities on the...
3 months ago 02:57
02:57
How to Track Any File?
In this video, we will show you how to use Canary Tokens to protect your...
3 months ago 13:32
13:32
Roskomnadzor's Secret Documents: Who and How Spies on Russians Online
Vladimir Putin's illnesses, the crimes of the Russian army in Ukraine, criticism of the Kremlin...
3 months ago 00:41
00:41
A Wi-Fi router can spy on you
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 08:40
08:40
What Stories Does Investigative Journalism Tell?
Journalist Janine Louloudi explores data-driven investigations into complex areas such as using artificial intelligence to...
5 months ago 47:01
47:01
Encryption vs. Government Surveillance
The CEOs of Signal, WhatsApp, Matrix, and Element discuss how to encrypt messaging apps. Governments...
5 months ago 46:35
46:35
World Uyghur Congress President on China's Digital Surveillance
World Uyghur Congress President Dolkun Isa talks about China’s surveillance of Uyghurs in Xinjiang. Since...
5 months ago