Filters
 17:37
17:37
You need anonymity online. And that's why
Anonymity on the Internet is not only a tool of hackers, but also a key...
1 month ago 09:47
09:47
2025 in Review: Anyone Can Be Labeled a Spy
A review of 2025 for the human rights project Perviy Otdel (“First Department”) and for...
2 months ago 11:30
11:30
THE HYDROGEN BOMB AND THE MEMORIAL. Academician Sakharov
Academician Sakharov is loved for different things: some know him as the creator of the...
2 months ago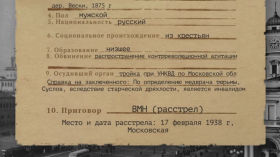 08:51
08:51
Secret archives of the secret services
The Russian state does not like to explain why it persecutes this or that person....
2 months ago 29:56
29:56
Venny Ala-Siurua, Women on Web: How Nonprofits Can Protect Themselves from Cyberattacks and Blocks
eQtalk is an original project of the eQtv channel. Special issue with Leonid Yuldashev, coordinator...
3 months ago 07:56
07:56
Documenting war crimes
Latvian investigative journalist Inga Springe talks about her passion and power to change the world...
3 months ago 35:45
35:45
Invisible War: How Drones Were Used in FATA (Pakistan)
Life in Pakistan's FATA (Tribal Areas) and why US drone strikes there have gone unseen....
4 months ago 05:51
05:51
The Syrian Archive. How Photos and Videos Help Document Human Rights Violations in Syria
Why is it important to collect video and photo evidence of human rights violations? What...
5 months ago 47:06
47:06
Google, Discord and TikTok on Protecting Users Online
Google, Discord, and TikTok employees discuss industry standards for trust and safety in the digital...
5 months ago 30:49
30:49
Signal President on threats to encrypted messaging
Signal President Meredith Whittaker and former Wired Editor-in-Chief Gideon Litchfield discuss the importance of end-to-end...
5 months ago 31:27
31:27
The Universal Declaration of Human Rights and New Digital Technologies
Volker Türk, UN High Commissioner for Human Rights, and Marwa Fatafta of Access Now discuss...
5 months ago 30:06
30:06
How to Avoid Shutdown
Peggy Hicks of the Office of the UN High Commissioner for Human Rights and Berhan...
5 months ago 13:50
13:50
Without a license and a passport. Who are stateless people?
Can your Russian passport be taken away for an anti-war post on the Internet? According...
5 months ago 43:56
43:56
25 Years of Fighting the FSB. Counterintelligence from the inside. Lawyer Ivan Pavlov
In the 2000s, they tried to kill him; in the 2010s, they planted bugs and...
5 months ago 12:28
12:28
Political Repression in the Soviet Union
After the Red Revolution, Russia regularly experienced waves of extermination of enemies of the state....
5 months ago 12:08
12:08
Political Investigation in the Russian Empire
In 1649, at the people's request, the government issued the Cathedral Code, the first Russian...
5 months ago 11:15
11:15
Hands off: how to withdraw consent to biometrics processing
Have you submitted your biometrics to your bank? In the near future, it will be...
5 months ago 14:03
14:03
Shutting down the Internet - when, how and for what? | Shakedown, Part 1
A complete shutdown of the Internet - what is it like? We are used to...
5 months ago 02:21
02:21
Bringing human rights standards to content moderation on social media
The problems of content moderation in social networks can be solved by creating a "social...
 03:25
03:25
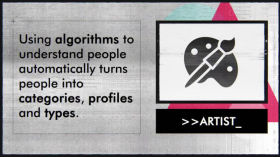
How to Create and Use Algorithms?
Using algorithms, you can reduce the time it takes to complete many tasks. However, you...
