Filters
 06:12
06:12
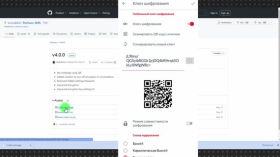
Guerrilla texting: encrypted text messages in case of an internet outage.
The probability of Internet shutdown in Russia is high, but we can say with a...
4 weeks ago 00:33
00:33
Puter. Operating system in a browser
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 weeks ago 00:32
00:32
Best Free AI Tools in 2024
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
1 month ago 25:10
25:10
"If we don't give up users, we'll be shut down." A conversation about Telegram, the FSB, and state defense procurement
The main character of the investigation by "Important Stories" about the connection between Telegram and...
1 month ago 01:15:11
01:15:11
Privacy in the age of AI
A recording of a community call dedicated to the future of DAOs (Decentralized Autonomous Organizations—organizations...
1 month ago 49:20
49:20
Robots: What We've Taught Them Over the Last 100 Years
How robots evolved from the heavy automatons of the 18th century to today's smart and...
2 months ago 15:14
15:14
Prayer and scammers. How they steal money and data in prayer groups.
In prayer publics, they quote the Bible, publish prayers for all occasions. And they pray...
2 months ago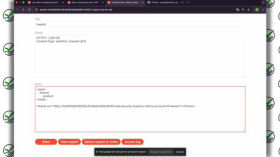 11:08
11:08
Getting ready for cybersecurity certification — Lab 27 (Clickjacking): How hackers trick you into clicking links
Getting ready to obtain a cybersecurity certification together by solving lab exercises. The labs used...
2 months ago 00:38
00:38
Historical Cartography
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 16:22
16:22
Battle for Soledar in Minecraft. Cybersports and Russian propaganda
How does Russia use eSports to spread its propaganda? And why are video games a...
2 months ago 52:47
52:47
Why Telegram has Become the Center of Digital Life
How Telegram works and what makes it stand out among other digital platforms, besides the...
2 months ago 00:33
00:33
Resources that will make your life easier
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago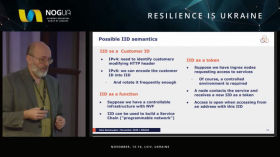 38:59
38:59
What IPv4 can't do?
IPv4 continues to operate in Ukraine, but its capabilities are already limited due to the...
2 months ago 23:43
23:43
Artificial Intelligence. How Russia uses AI in information warfare
Russia is already using artificial intelligence in the war against Ukraine. To promote fakes and...
2 months ago 45:29
45:29
How do we manipulate with the truth?
Is it possible to recognize an expert? Or is it still a utopia? How do...
2 months ago 00:39
00:39
Which Antivirus is the Best?
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 10:17
10:17
Hedra AI, LivePortrait, Heygen Expressive Photo Avatar: Best Tools for Facial Animation
A review of three of the newest and best neural networks for face animation. From...
2 months ago 46:05
46:05
Artificial Intelligence: Can Machines Think Like Humans?
AI is already capable of what was long considered uniquely human: creating texts, solving problems,...
2 months ago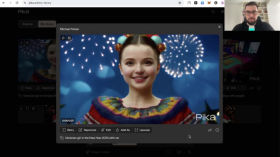 16:30
16:30
Pika Art - a neural network for video generation
Pika is a neural network video platform. Here pictures are "animated" and videos are created...
2 months ago 01:28
01:28
How does CERT-UA help energy companies, why is it important to connect to MISP?
Ukraine's energy facilities are hackers' top targets. CERT-UA's Evgeniy Briksin explains how the MISP platform...
2 months ago