Filters
 17:33
17:33
How Microsoft Will Force You to Abandon Windows 10
Windows 10 is officially becoming a thing of the past: security updates are ending, and...
3 weeks ago 13:16
13:16
How Adult Sites Collect and Sell Your Data — and What to Do About It
An analysis of the investigation by Microsoft Research about how the industry entertains some —...
4 weeks ago 42:48
42:48
Blockchain, AR/VR and Artificial Intelligence – What Has Changed in Five Years?
On the podcast's fifth anniversary, host Samat Galimov meets with guests from previous episodes to...
2 months ago 20:22
20:22
A Practical Guide to Building an AI Agent in Copilot
The video demonstrates the process of creating and configuring AI agents in Copilot. It covers...
2 months ago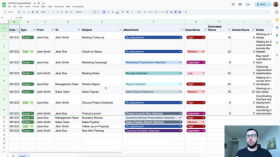 15:08
15:08
Gemini Workspace - work in Google Sheets, Docs, Slides
Gemini for Workspace - AI capabilities in Google Sheets, Docs, Slides, and Mail. Convenience of...
2 months ago 51:52
51:52
Copilot: Complete Guide to Using It in 2026
A detailed guide to Microsoft Copilot 365 and its capabilities in 2026. The video covers...
2 months ago 00:47
00:47
Why pirated Windows is updated
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 23:36
23:36
ChatGPT is not alone. Top 5 neural networks to improve your performance
TOP 5 neural networks for increasing efficiency. AI for text. Video, audio generation. Neural networks...
5 months ago 19:02
19:02
Microsoft Copilot Pro - creating presentations for Word, Excel, PowerPoint
Microsoft Copilot Pro integrates ChatGPT into Word, Excel, and PowerPoint to create presentations and generate...
5 months ago 22:11
22:11
Microsoft Copilot - a personal assistant from Microsoft
A complete guide to using Microsoft Copilot. Creating personal assistants from Microsoft. What is Bing...
5 months ago 47:19
47:19
Microsoft and Access Now on How Tech Companies Respond to Crises
Experts from Microsoft and Access Now discuss a timely topic: how tech companies and civil...
5 months ago 04:00
04:00
How to restore Microsoft Authenticator codes on another device
What do you do if you've lost your phone, had your phone stolen, or just...
5 months ago 05:22
05:22
Passkey: Passwordless authorization by location
Passkey cannot be called a completely new authorization method, but given that today not many...
5 months ago 56:01
56:01
Why are our Devices so Hard to Fix?
Right to repair is the idea that users should be able to decide for themselves...
8 months ago