First Department
127 videos
 09:47
09:47
2025 in Review: Anyone Can Be Labeled a Spy
A review of 2025 for the human rights project Perviy Otdel (“First Department”) and for...
2 months ago 22:34
22:34
18,000 Glasses of Water and an SUV for 80 Rubles: How AI Agents Go Crazy
More and more people and companies are asking whether artificial intelligence can replace a human...
2 months ago 16:04
16:04
The Quietest Cyber Catastrophe of 2025
You might think you use only safe, licensed software and know exactly where it comes...
1 month ago 17:33
17:33
How Microsoft Will Force You to Abandon Windows 10
Windows 10 is officially becoming a thing of the past: security updates are ending, and...
3 weeks ago 16:35
16:35
New Roskomnadzor Rules: How Are We Supposed to Live?
“Roskomnadzor has received new powers and can now block EVEN MORE!” — headlines like these...
3 months ago 18:29
18:29
How Digital Racism Works
AI is increasingly being used for racial segregation and political control — from “smart” surveillance...
2 months ago 18:27
18:27
How Unrestricted AI Helps Criminals
Artificial intelligence has become a convenient tool for hackers and cybercriminals. We’re talking about “smart...
3 months ago 17:44
17:44
Who Needs the Darknet and How to Use It
Everyone from 8 months to 88 years old “knows” that the dark net is a...
2 months ago 29:28
29:28
We were attacked by Kremlin hackers. Let's respond.
Code red: Russian special services are massively attacking civil society. Hackers are trying to quietly...
5 months ago 11:41
11:41
Yandex has been added to the surveillance registry. Again
Over the course of this year, 9 Yandex services have been included in the register...
5 months ago 13:53
13:53
How russia today made the 4chan conspiracy theory a reality.
A Russian bot farm created by the FSB and Russia Today was active on Twitter,...
5 months ago 54:36
54:36
Gadget for Hacking Any Smartphone. Mobile Forensic Expert and UFED
Russian security forces can hack any phone and gain access to your correspondence using automated...
4 months ago 18:47
18:47
How to Protect Your Data | A Guide to Security Basics
In today's world, your data is the new oil, and cyberspace has become a battlefield....
5 months ago 10:50
10:50
How to Choose a VPN to Bypass Blockages and Encrypt Traffic
Russia has been censoring and blocking websites for a decade, and since the start of...
1 month ago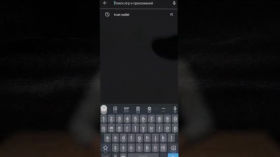 10:50
10:50
Cryptocurrencies: How to Survive without Banks Abroad and at Home
Cryptocurrencies are decentralized electronic money that, unlike fiat currencies, are not controlled by governments or...
1 month ago 17:37
17:37
You need anonymity online. And that's why
Anonymity on the Internet is not only a tool of hackers, but also a key...
1 month ago 19:22
19:22
The all-seeing eye? How surveillance and facial recognition works
In Moscow, surveillance cameras with a facial recognition system are widely used, actively used for...
2 months ago 17:06
17:06
The Cheburnet is coming! We tell you where Roskomnadzor came from.
Roskomnadzor blocked it - this wording has become the norm for the Russian Internet. About...
5 months ago 14:30
14:30
Without a face: why the state needs your biometrics
At the end of 2022, a law on biometric data was adopted in Russia, which...
5 months ago 12:33
12:33
New Pegasus attacks. Who was hacked this time?
The world's most famous spyware strikes again! Since the release of the previous "First Section"...
2 months ago 18:48
18:48
The truth about Roskomnadzor's secret department
Belarusian hackers have broken into the internal network of Roskomnadzor, revealing the Kremlin's plans for...
5 months ago 13:59
13:59
Get off the radar! How not to give away your location to anyone
Right now, anyone can find out where you are. Not just intelligence officers, but also...
5 months ago 12:15
12:15
Phishing attacks: how scammers get your data
Phishing is a common form of Internet fraud in which attackers pose as trusted sources...
2 months ago 12:33
12:33
Hiding data. The method of secret services. Steganography
You probably know that to protect sensitive data, you need to store it on an...
5 months ago 13:55
13:55
What is a bot farm and what do Ilon Musk and neural networks have to do with it?
Who are bots and trolls, what is the difference between them, and how bot farms...
5 months ago 10:25
10:25
Cheburnet by passport? Sovereign Internet Project
Russia is planning to implement a real Cheburnet, just like in North Korea — at...
1 month ago 20:14
20:14
Telegram meta-universe. How law enforcement agencies find you
Since Pavel Durov's arrest in Paris, Russian and foreign media have published numerous articles about...
2 months ago 14:44
14:44
How Rostelecom built a digital gulag.
Thanks to their work, you have internet at home, no matter where your home is...
5 months ago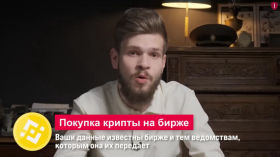 12:56
12:56
Donate Safely! How Security Forces Track Crypto
Recently, the FSB announced that it had detained a Russian accused of treason for transferring...
2 months ago 11:23
11:23
How VKontakte is (still) jailing users
The social network VKontakte is a dangerous place. Careless words can lead to criminal charges,...
5 months ago 12:22
12:22
TOR BROWSER | The first step to true anonymity online
If you seriously need to hide your presence on the network, a regular VPN may...
5 months ago 11:00
11:00
Learn to encrypt your PC and smartphone in 11 minutes. Instruction for beginners
Is there a password on your device to log in? Don't rush to think that...
5 months ago 19:19
19:19
SECURE MESSENGER. The best programs for secret correspondence
In order for your correspondence not to be read by special services or other intruders,...
5 months ago 12:10
12:10
Cryptography. Debunking the myth of omnipotent intelligence services
"There's no point in defending yourself, the FSB has access to everything anyway" - these...
2 months ago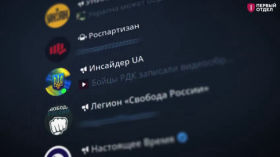 32:16
32:16
“Cards, Wagner, two computers": how a Kuban sysadmin outplayed the FSB (and didn't go to jail).
Russian hackers, PMC "Wagner", recruitment and change of state. All these topics are intertwined in...
5 months ago 14:33
14:33
Why do you need an anonymous phone number (and where to get it)?
Calling on a regular phone is a thing of the past! Today, a phone is...
5 months ago 18:37
18:37
The secret to advanced anonymity! Install Whonix
If you need anonymity on the network not for the sake of interest, but for...
3 months ago 17:11
17:11
Publishing anonymously! How to write about important things - and not give yourself away
There are a lot of taboo topics in Russia. War cannot be called war, corruption...
5 months ago 10:00
10:00
Dangerous comments! What, where and how to post on YouTube?
Is it possible to write these or other things in the comments? And in general,...
3 months ago 13:37
13:37
A strong password. Explained in 13 minutes and 37 seconds
Passwords - how to come up with them correctly and exactly how to use them....
5 months ago 09:37
09:37
Cameras with facial recognition now in every city
Total surveillance - in every city! The Ministry of Statistics wants to centralize many existing...
5 months ago 15:40
15:40
AI in the service of dictatorships. When to expect a machine uprising?
The European Union recently passed a law on the regulation of artificial intelligence — the...
5 months ago 10:48
10:48
How a “smart camera” almost put an innocent man in jail.
To penetrate the secrets of the past and solve old cases, Russian security forces decided...
5 months ago 17:55
17:55
Splinternet. How is the internet being divided and what can we do about it?
The global network has become such an integral part of our lives that we cannot...
5 months ago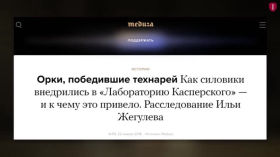 16:06
16:06
Antiviruses. To install or not to install?
"The border is locked, but the enemy is already inside" - this is how one...
5 months ago 11:25
11:25
FSB-taxi: special services will trace your every trip
The FSB will be able to monitor your every taxi ride. According to the new...
2 months ago 11:36
11:36
Sovereign digital certificates. What is it and why?
Russian banks have begun to demand digital certificates from the Ministry of Digital Development, without...
2 months ago 11:50
11:50
Quantum computer will reveal ALL your secrets (one day)
In the next 10-15 years, we will experience a quantum revolution - no, not like...
2 months ago 12:34
12:34
The dangers of smart devices
If you sometimes feel like your TV is spying on you, or your smart fridge...
5 months ago 13:58
13:58
How do they calculate anonymous authors? Let's talk about stylometry
How to identify an anonymous author if they left no digital trace? You need to...
5 months ago 21:57
21:57
How can any phone be hacked? The elusive Pegasus.
Pegasus is the most famous hacker software in the world, which almost everyone has heard...
2 months ago 13:19
13:19
How are Telegram users de-anonymized? The Laplace demon.
It has long been known that Telegram users can be de-anonymized using leaked databases of...
5 months ago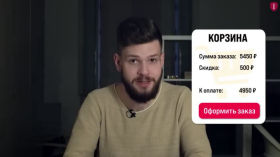 14:37
14:37
Are neural networks starting to show character? AI preferences
It's time to uncover the secrets of the digital "soul" of artificial intelligence and answer...
2 months ago 13:04
13:04
Phishing: how scammers steal money and data
One of the most common cyber attacks is phishing. Attackers lure you to a fake...
5 months ago 15:07
15:07
Who ordered total surveillance? Rostec Corporation.
Rostec is known among the people for its constant advertising of “the most modern weapons,...
5 months ago 14:58
14:58
How do you know if your phone has been hacked?
Most of you store your most valuable data on your phone: correspondence, routes, payment information,...
1 month ago 11:59
11:59
Healthy hackers - why are they being banned?
There's a heated debate going on again in government: should we allow "white hat" hackers...
5 months ago 13:41
13:41
What is the danger of the Russian app store RuStore?
When you buy a phone, it already has many applications installed. Games, social networks, manufacturer's...
4 weeks ago 20:46
20:46
Deepfake is walking the planet! How AI is changing politics
Replacing voices and faces with AI is not a new thing and is loved by...
1 month ago 11:52
11:52
How your data is being sold. Protecting yourself from breaches
Your data is being traded on the Internet. Moreover, a criminal can buy not only...
2 months ago 18:16
18:16
We studied internet censorship around the world and here's what we realized
Internet censorship review from the First Department. Who, how and why is breaking our Internet?...
5 months ago 11:15
11:15
Hands off: how to withdraw consent to biometrics processing
Have you submitted your biometrics to your bank? In the near future, it will be...
5 months ago 13:18
13:18
Signal vs. Roskomnadzor. Getting around blocking
Roskomnadzor learned about the existence of secure messengers and decided to declare war on them....
5 months ago 16:42
16:42
Don't tell AI your secrets
Artificial intelligence is marching across the planet! Not a week goes by without the launch...
5 months ago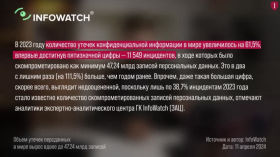 21:57
21:57
THIS IS A BASE. And it's leaked.
140 million — that's how many phone numbers of Russians leaked online in 2024. One...
5 months ago 23:19
23:19
Tails is ultimatum security on Snowden's orders
How to go online without leaving a trace? Is it possible to publish something while...
5 months ago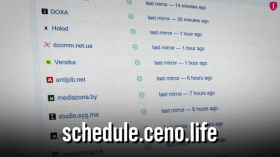 16:28
16:28
These apps will save you if the internet goes down | Shakedown, Part 2
The first part of the video about the shutdown told about the conditions under which...
5 months ago 17:30
17:30
The 5 rules of email security. Save yourself from being hacked
The British have a favorite dish - fish and chips, and the Kremlin hackers -...
5 months ago 25:04
25:04
DEGUGLIZATION. Replace services with more confidential ones
User data is a precious resource that all major IT companies dream of getting their...
5 months ago 17:37
17:37
Global surveillance system. Project ESHELON.
In the 1960s, the intelligence services of the five English-speaking NATO countries launched a joint...
5 months ago 37:55
37:55
How a programmer disrupted an FSB special operation and revealed their most important secret
FSB operatives made programmer Kirill Parubets an offer he couldn't refuse: put your friend in...
5 months ago 16:34
16:34
Blocking Calls in WhatsApp and Telegram: Causes, Consequences and Solutions
WhatsApp and Telegram calls have stopped working in Russia. The authorities justify this with “security...
2 months ago 30:44
30:44
Messenger for paranoid people. Customizing SimpleX Chat
This is a complete guide to using SimpleX Chat, one of the most secure messengers...
2 months ago 23:18
23:18
Harmful advice: watch this video and do the opposite
Today and only today you have a unique opportunity to refuse to protect your data...
5 months ago 26:58
26:58
Cyberattacks and negligence: lessons for millions of dollars
How to lose data through banal human negligence and carelessness? How to protect yourself? Why...
5 months ago 07:52
07:52
Why do intelligence agencies need spyware?
We are all being listened to by SORM, a system for intercepting phone calls and...
2 months ago 07:16
07:16
How to protect your privacy? Kirill Parubets, Mikhail Svetov
Programmer Kirill Parubets was forced to cooperate by the FSB, and the Monocle spyware was...
5 months ago 16:24
16:24
How the FSB recruits. The story of Kirill Parubets
Programmer Kirill Parubets was detained by the FSB and given an offer that is hard...
5 months ago 08:34
08:34
Spoiling FSB professional holiday (3 years in a row)
December 20 is “Chekist Day” in Russia, a professional holiday for the state security agencies....
2 months ago 26:58
26:58
Legendary hacker Kevin Mitnick
The story of Kevin Mitnick, one of the most famous hackers in history. He became...
5 months ago 36:32
36:32
How intelligence agencies control mass consciousness
Psyops. Active measures. Assistance operations. All these words are used to describe roughly the same...
2 months ago 14:58
14:58
Why doesn't Roskomnadzor notice drug shops?
Traders of prohibited goods on the darknet have long revealed the secrets of resisting censorship....
2 months ago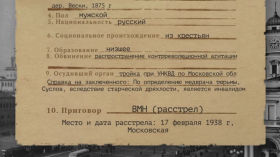 08:51
08:51
Secret archives of the secret services
The Russian state does not like to explain why it persecutes this or that person....
2 months ago 06:40
06:40
OPM and you: what's important to know
What do police officers do when they wiretap your phone, sit in your car outside...
5 months ago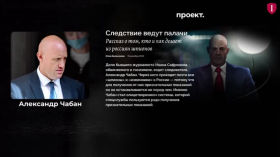 06:25
06:25
Treason against the Motherland. From state secrets to SMS
Since 2014, FSB investigators have been increasingly registering citizens as traitors to the state, and...
5 months ago 12:28
12:28
Political Repression in the Soviet Union
After the Red Revolution, Russia regularly experienced waves of extermination of enemies of the state....
5 months ago 12:08
12:08
Political Investigation in the Russian Empire
In 1649, at the people's request, the government issued the Cathedral Code, the first Russian...
5 months ago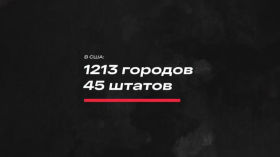 06:54
06:54
How social media changed protest
It is very difficult to imagine life without social networks. Through them we meet, communicate,...
5 months ago 08:20
08:20
The life (and death) of real spies
Russia is gripped by spy mania - the FSB is looking for secret agents of...
5 months ago 07:36
07:36
Big Laundry. The Art of Money Laundering
The term “money laundering” has been around for over 80 years, and there are countless...
5 months ago 10:05
10:05
Big Brother. History of surveillance
Holmes versus Moriarty. Bastrykin versus a magnifying glass. Aristotle versus a press with spikes. The...
2 months ago 11:30
11:30
THE HYDROGEN BOMB AND THE MEMORIAL. Academician Sakharov
Academician Sakharov is loved for different things: some know him as the creator of the...
2 months ago 13:56
13:56
Made in China: how China is exporting a digital dictatorship
Where did all these Chinese surveillance cameras come from? It’s simple: China is actively exporting...
5 months ago 19:33
19:33
The service of “bad Russians”. What Rossotrudnichestvo does
While the FSB, the Ministry of Defense, and Russian courts compete for the worst reputation,...
2 months ago 15:48
15:48
How Ekaterina Mizulina became an Internet celebrity
Little is usually known about the lives of children of officials. If something comes to...
5 months ago 13:48
13:48
WITNESSES OF THE USSR | Why don't they pay taxes, loans, don't recognize courts and what's wrong with it?
Did you know that Russia doesn't really exist? Yes, there is no such country on...
4 months ago 13:50
13:50
Without a license and a passport. Who are stateless people?
Can your Russian passport be taken away for an anti-war post on the Internet? According...
5 months ago 11:54
11:54
How the U.S. Ambassador Was Spied on for 7 Years with an Invisible Bug—and Its Surprising Link to Electronic Music
In 1945, Soviet spies scored a major victory over their American colleagues: they managed to...
2 months ago 31:10
31:10
ENIGMA. How the “invincible” cipher was cracked
How did Enigma work, why was it needed in the first place — and how...
5 months ago 43:56
43:56
25 Years of Fighting the FSB. Counterintelligence from the inside. Lawyer Ivan Pavlov
In the 2000s, they tried to kill him; in the 2010s, they planted bugs and...
5 months ago 21:00
21:00
Back to the USSR: FSB against the enemies of the people.
The concept of "Motherland" is nurtured in each of us from early childhood. To be...
5 months ago 13:20
13:20
Secrets of the FSB: Why do they hide archives?
The main Russian special service inherited the archives of the Cheka, NKVD and KGB -...
5 months ago 10:43
10:43
Why Piracy Is Bad For You, Not Just Developers
Russia is one of the world leaders… in the field of piracy. Only China is...
5 months ago 13:07
13:07
How China is spying on users around the world
"Chinese Big Brother" spies on people not only in China but also abroad. How Chinese...
5 months ago 13:39
13:39
JAIL FOR A GPS TRACKER?! Let's study spy gadgets
Did you know that Russian security forces can cause you problems because of a simple...
5 months ago 15:24
15:24
Complete internet blackout. What to do?
You use the internet every day — but what happens if the government pulls the...
5 months ago 22:07
22:07
How your smartphone keyboard is spying on you.
The virtual or on-screen keyboard on your phone knows too much about you. And in...
5 months ago 22:05
22:05
China is erasing its own and our memory. What happened in Tiananmen Square?
The massacre of protesters in Tiananmen Square in 1989 is one of the most famous...
5 months ago 21:08
21:08
AI knows everything about you. And it doesn't like you.
Artificial intelligence, in addition to its positive applications in saving lives and creating content, is...
5 months ago 13:16
13:16
How Adult Sites Collect and Sell Your Data — and What to Do About It
An analysis of the investigation by Microsoft Research about how the industry entertains some —...
1 month ago 24:00
24:00
Hacked a bank = bought a rocket. How DPRK hackers work
North Korean hackers have become a state agency, generating revenue for the country, evading sanctions...
5 months ago 20:33
20:33
The most honest review of the MAX messenger
In this video, "The First Department" examines how secure the MAX messenger is. We find...
1 month ago 21:22
21:22
How hackers started a global cyber war
North Korean hackers steal billions via SWIFT and crypto. Chinese hackers attack big pharma and...
5 months ago 19:08
19:08
Surveillance of dissenters... IN EUROPE?
Pegasus spyware is usually discussed in the context of dictatorships: some autocrat is spying on...
5 months ago 20:12
20:12
Why do ordinary people need cybersecurity?
Want to understand how to protect your data, why and from whom — and whether...
5 months ago 22:46
22:46
Everything You Wanted to Know About Starlink
This video covers everything you need to know about Starlink satellite internet: how Elon Musk's...
2 months ago 18:31
18:31
The free internet in Russia has come to an end
The free internet in Russia is dying right before our eyes. Once one of the...
5 months ago 38:47
38:47
Concentration camp in DNR, Ukrainian “spy”, Lamborghini for militants | The story of Alexander Marchenko.
Alexander Marchenko is a Ukrainian serving a sentence in Russia on trumped-up charges of espionage....
2 months ago 17:28
17:28
CENSORSHIP: from book burning to Roskomnadzor
There is one tradition: to burn archives and pretend that nothing happened before. It began...
5 months ago 29:55
29:55
E-mail is the middle ground between a safe and a dumpster. How to fix it?
Email is one of the oldest and most boring web technologies that most users prefer...
1 month ago 12:51
12:51
YouTube and Wikis will be blocked - but what will be left in return?
The Last of Us. Kings of the Hill. Veterans of the Resistance. YouTube and Wikipedia....
4 months ago 10:08
10:08
They will know about all your movements in Russia.
The Ministry of Transport is planning to increase the amount of surveillance in transport by...
5 months ago 14:03
14:03
Shutting down the Internet - when, how and for what? | Shakedown, Part 1
A complete shutdown of the Internet - what is it like? We are used to...
5 months ago 08:04
08:04
Bypassing blocking - banned content. Can we get out of this?
From March 1, 2024, Roskomnadzor will begin to block instructions for bypassing the blocks. In...
1 month ago 11:50
11:50
Why Discord isn't safe, even if you only need it for gaming
After our video about messengers, many of you asked: what is Discord dangerous, and why...
5 months ago 01:49:37
01:49:37
How the FSB Failed a Special Operation with an IT Specialist from Ukraine. Operation "Monocle"
The Role of Cyber Operations in Modern [Counter]Intelligence. The Ethical Dilemma of Maintaining a Balance...
5 months ago 12:20
12:20
Why are deepfakes dangerous?
Neural networks can generate photorealistic images, compose music, imitate voices, and even create videos. This...
5 months ago