Filters
 05:27
05:27
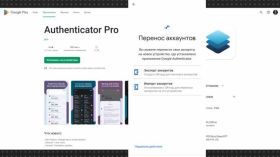
Authenticator Pro: review of two-factor authentication app for Android
There are quite a few apps for two-factor authentication. The most popular one, Google Authenticator,...
1 month ago 13:58
13:58
Safe Mode: How to Protect Your Communications
If you live in Russia, you've probably been hacked at least once — or at...
1 month ago 05:01
05:01
How to recover codes from Google Authenticator on another phone
Two-factor authentication should be enabled on all sensitive accounts - it's the law. One of...
2 months ago 01:04:01
01:04:01
Pavel Belousov, Nadiyno.org: Basic rules of digital hygiene for your safety
Pavel Belousov, tech lead for the Nadiyno.org digital help hotline, gives recommendations on how to...
5 months ago 02:35
02:35
How to strengthen the protection of company information resources and employee accounts?
Reliable cybersecurity is a task for everyone, not just government agencies. Evgeniy Briksin from CERT-UA...
5 months ago 01:19
01:19
Can hackers access your messengers?
If your device doesn't have a password or two-factor authentication, attackers can access messengers, including...
5 months ago 02:28
02:28
Multi-factor authentication to protect your accounts
Digital security course: how to use MFA, why is it needed
5 months ago 25:04
25:04
DEGUGLIZATION. Replace services with more confidential ones
User data is a precious resource that all major IT companies dream of getting their...
5 months ago 18:47
18:47
How to Protect Your Data | A Guide to Security Basics
In today's world, your data is the new oil, and cyberspace has become a battlefield....
5 months ago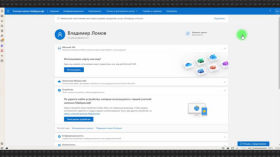 04:00
04:00
How to restore Microsoft Authenticator codes on another device
What do you do if you've lost your phone, had your phone stolen, or just...
5 months ago 03:40
03:40
What to do if Your Telegram is Hacked?
Has your Telegram been hacked? Don't panic! In this video, we'll tell you what to...
5 months ago 40:33
40:33
Are Passwords Out of Date? Let's Talk Authentication
Passwords are no longer considered reliable protection. Samat Galimov and information security expert Karim Valiev...
7 months ago 07:57
07:57
Cybersecurity cert prep: Lab 16 (Auth) — bypass MFA and save sessions using Python requests
Getting ready to obtain a cybersecurity certification together by solving lab exercises. The labs used...
