Filters
 00:37
00:37
Privacy, settings and leaks
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
3 weeks ago 01:02:26
01:02:26
Oleksandr Glushchenko, Pavlo Belousov: MAХ messenger – delete it IMMEDIATELY!
Pavel Belousov, technical lead for the Nadiyno.org digital help hotline, gives recommendations to Internet users:...
4 weeks ago 00:41
00:41
Refuting the "Reserve+" leak
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 00:39
00:39
Which Antivirus is the Best?
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 00:36
00:36
Downloading From the Internet and Checking Links
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago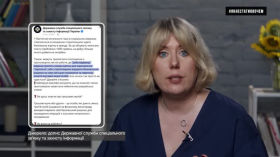 14:26
14:26
The danger of social networks
We continue to understand how scammers operate and how to protect yourself from fraudulent schemes...
2 months ago 05:11
05:11
HTTP or HTTPS – How Does it Work and What is the Difference?
In this video, we'll cover the basics of how the internet works and how using...
3 months ago 02:57
02:57
How to Track Any File?
In this video, we will show you how to use Canary Tokens to protect your...
3 months ago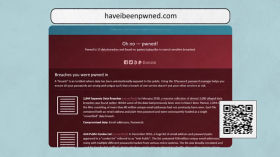 01:32
01:32
Have I been hacked
Digital security course: How to hack someone's account, how to understand whether it's reliably protected...
4 months ago 02:14
02:14
How to Create and Keep Strong Passwords
Digital security course: How to create and store strong passwords
4 months ago 00:33
00:33
Private data in someone else's hands
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 00:35
00:35
Watch Dogs in Ukrainian
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 00:37
00:37
Checking a receipt for payment via the Internet
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 00:31
00:31
What happens if you log into someone else's account without permission
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 00:39
00:39
What information about you is collected by scammers
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 00:43
00:43
We Calculate Scammers Using AI
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 01:06:50
01:06:50
Distributed services, self-hosted and open source will save us. Or not
Discussion of IT solutions independent of jurisdictions and corporations in the context of sanctions and...
5 months ago 03:05
03:05
How Can Your Selfie be used Against You?
Who can use your selfie and how? What is verification and identification? What are the...
5 months ago 13:13
13:13
Paid 50000 UAH and silence. Top cheating schemes in Instagram
Every day we risk losing our money due to increasingly sophisticated fraudulent schemes on social...
5 months ago
