Filters
 00:37
00:37
Privacy, settings and leaks
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 weeks ago 34:28
34:28
What you need to know about smartphone security on the go
Discussion of measures of digital security in the context of mobilization in Russia September 21,...
4 weeks ago 13:41
13:41
What is the danger of the Russian app store RuStore?
When you buy a phone, it already has many applications installed. Games, social networks, manufacturer's...
4 weeks ago 13:16
13:16
How Adult Sites Collect and Sell Your Data — and What to Do About It
An analysis of the investigation by Microsoft Research about how the industry entertains some —...
1 month ago 14:58
14:58
How do you know if your phone has been hacked?
Most of you store your most valuable data on your phone: correspondence, routes, payment information,...
1 month ago 00:33
00:33
What data about yourself can be found online and deleted
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
1 month ago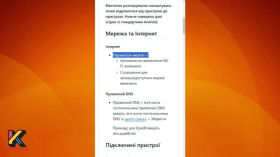 00:32
00:32
Privacy Settings for Popular Services
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
1 month ago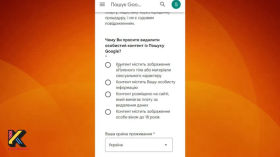 00:33
00:33
How to Delete Information About Yourself From Google
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
1 month ago 01:15:11
01:15:11
Privacy in the age of AI
A recording of a community call dedicated to the future of DAOs (Decentralized Autonomous Organizations—organizations...
1 month ago 04:00
04:00
Tips from Nadiyno.org: what personal information should never be disclosed online
Useful tips from the Nadiyno.org digital assistance hotline. Pavlo Bilousov, the hotline's technical expert, answers...
1 month ago 07:36
07:36
How to Hide Apps and Files on Your Smartphone
An overview of reliable ways to hide personal apps, photos, and data on Android and...
2 months ago 25:47
25:47
LLM in Your Own Data Center: An AI Solution for Operators Deployed on Their Own Networks
LLM solutions in their own data center in Ukraine allow operators to run AI without...
2 months ago 26:05
26:05
Data Journalism vs. Big Tech
Nabiha Sayed, CEO of The Markup, discusses how her nonprofit news organization combines data journalism...
2 months ago 14:37
14:37
Are neural networks starting to show character? AI preferences
It's time to uncover the secrets of the digital "soul" of artificial intelligence and answer...
2 months ago 00:35
00:35
Visualizing our text files
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
2 months ago 11:50
11:50
Quantum computer will reveal ALL your secrets (one day)
In the next 10-15 years, we will experience a quantum revolution - no, not like...
2 months ago 10:05
10:05
Big Brother. History of surveillance
Holmes versus Moriarty. Bastrykin versus a magnifying glass. Aristotle versus a press with spikes. The...
2 months ago 13:41
13:41
Chrome is out of Fashion? Here are the Top 10 More Interesting Options!
Google Chrome holds 66% of the browser market, but should you trust it? In this...
2 months ago 24:31
24:31
Cybersecurity cert prep: Lab 30: SQL Injection — Reveal hidden items with Python automation
Getting ready to obtain a cybersecurity certification together by solving lab exercises. The labs used...
2 months ago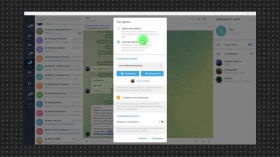 04:06
04:06
Gretel bot in Telegram will remove you from all pre-selected groups in case of danger
Telegram bot Gretel_sos_bot is designed to perform just one simple function, but it can cost...
2 months ago