Filters
 06:12
06:12
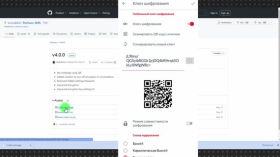
Guerrilla texting: encrypted text messages in case of an internet outage.
The probability of Internet shutdown in Russia is high, but we can say with a...
4 weeks ago 06:08
06:08
Element messenger on Matrix: free, anonymous, decentralized, with end-to-end encryption
Free, cross-platform, open source, end-to-end encryption by default, the ability to create private and public...
4 weeks ago 10:50
10:50
Cryptocurrencies: How to Survive without Banks Abroad and at Home
Cryptocurrencies are decentralized electronic money that, unlike fiat currencies, are not controlled by governments or...
1 month ago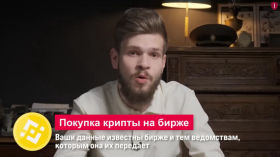 12:56
12:56
Donate Safely! How Security Forces Track Crypto
Recently, the FSB announced that it had detained a Russian accused of treason for transferring...
2 months ago 11:50
11:50
Quantum computer will reveal ALL your secrets (one day)
In the next 10-15 years, we will experience a quantum revolution - no, not like...
2 months ago 04:53
04:53
Tella: How to encrypt and hide files on Android and iPhone
In today's world, where digital security does not tolerate negligence, it is invaluable to have...
2 months ago 12:10
12:10
Cryptography. Debunking the myth of omnipotent intelligence services
"There's no point in defending yourself, the FSB has access to everything anyway" - these...
2 months ago 05:11
05:11
HTTP or HTTPS – How Does it Work and What is the Difference?
In this video, we'll cover the basics of how the internet works and how using...
3 months ago 00:43
00:43
We Are Looking for Miners on Your Computer
Short videos for every day: about useful applications, cybersecurity, artificial intelligence and OSINT.
4 months ago 01:24:04
01:24:04
Alexander Bornyakov, Ministry of Digital Development: on regulation of virtual assets in Ukraine, tax on crypto
Alexander Bornyakov on the regulation of virtual assets and taxes on cryptocurrency in Ukraine at...
5 months ago 30:49
30:49
Signal President on threats to encrypted messaging
Signal President Meredith Whittaker and former Wired Editor-in-Chief Gideon Litchfield discuss the importance of end-to-end...
5 months ago 47:01
47:01
Encryption vs. Government Surveillance
The CEOs of Signal, WhatsApp, Matrix, and Element discuss how to encrypt messaging apps. Governments...
5 months ago 02:35
02:35
How to communicate safely in messengers
Digital security course: How to communicate in messengers safely, which ones to choose and how...
5 months ago 07:47
07:47
How to secure your transfers and hide them from the state
Financial transfers in Russia have become completely unsafe: due to the “wrong” recipient, you may...
5 months ago 12:37
12:37
Safe Mode: How to Encrypt Your Data
What happens if your phone falls into the hands of criminals or, even worse, security...
5 months ago 31:10
31:10
ENIGMA. How the “invincible” cipher was cracked
How did Enigma work, why was it needed in the first place — and how...
5 months ago 07:36
07:36
Big Laundry. The Art of Money Laundering
The term “money laundering” has been around for over 80 years, and there are countless...
5 months ago 18:47
18:47
How to Protect Your Data | A Guide to Security Basics
In today's world, your data is the new oil, and cyberspace has become a battlefield....
5 months ago 11:00
11:00
Learn to encrypt your PC and smartphone in 11 minutes. Instruction for beginners
Is there a password on your device to log in? Don't rush to think that...
5 months ago 12:33
12:33
Hiding data. The method of secret services. Steganography
You probably know that to protect sensitive data, you need to store it on an...
5 months ago