Tactical Tech
22 videos
 29:25
29:25
Amateur Investigators Share Their Findings in Syria, Lebanon and Israel
Amateur investigators share their methods and experiences investigating three topics: where weapons come from in...
1 month ago 16:58
16:58
How Journalists Get Information and Investigate Cross-Border Crimes?
Romanian investigative journalist Paul Radu shares his methods for investigating corruption and organized crime, citing...
4 months ago 02:07
02:07
Human Influence on Software Algorithms
Writer, artist, and technologist James Bridle explores the possibilities and limitations of human-made algorithms and...
4 months ago 08:40
08:40
What Stories Does Investigative Journalism Tell?
Journalist Janine Louloudi explores data-driven investigations into complex areas such as using artificial intelligence to...
5 months ago 06:29
06:29
The Syrian Archive — Web Archive Documenting Human Rights Violations in Syria
Hadi al-Khatib explains how the Syrian Archive project works and why it is needed, helping...
5 months ago 07:56
07:56
Documenting war crimes
Latvian investigative journalist Inga Springe talks about her passion and power to change the world...
3 months ago 05:51
05:51
The Syrian Archive. How Photos and Videos Help Document Human Rights Violations in Syria
Why is it important to collect video and photo evidence of human rights violations? What...
5 months ago 35:45
35:45
Invisible War: How Drones Were Used in FATA (Pakistan)
Life in Pakistan's FATA (Tribal Areas) and why US drone strikes there have gone unseen....
4 months ago 02:54
02:54
How to Use Maps in Investigative Journalism?
Maps are an important tool in the hands of journalists and researchers. It is important...
5 months ago 10:59
10:59
Journalism During War in Ukraine
Journalist Lyubov Rakovitsa talks about the heavy burden of reporting on the war in Ukraine....
5 months ago 03:37
03:37
How to Start Investigating Companies?
Recommendations for novice investigators on how to start investigating companies. You can learn more about...
5 months ago 03:37
03:37
How to Collect and Verify Evidence?
What information is evidence, how should it be verified. What questions should be asked when...
4 months ago 03:10
03:10
What are the Risks for Investigative Journalists? How to Protect Yourself?
Investigative journalists often take risks and find themselves in danger. To protect yourself, you need...
2 months ago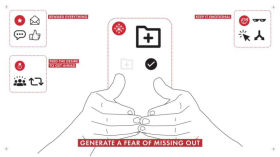 03:19
03:19
Six Easy Steps to Get Us Addicted To Our Phones
How and why we become addicted to our Phones
4 months ago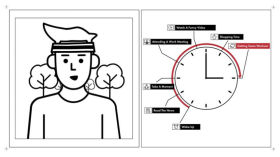 04:20
04:20
What Someone Can Learn About Your Day by Collecting Information from Your Devices?
When you interact with devices and platforms, you give them the opportunity to collect your...
2 months ago 02:58
02:58
How to Find and Recover Deleted Web Pages?
If web pages and content are removed from the Internet, they can still be restored...
2 months ago 03:05
03:05
How Can Your Selfie be used Against You?
Who can use your selfie and how? What is verification and identification? What are the...
5 months ago 03:00
03:00
Who has Access to your Personal Data?
When you allow health apps to access your personal data, do you think about what...
2 months ago 03:14
03:14
What Can Your Phone Number Say About You?
A phone number is a fairly unique piece of information that allows you to identify...
5 months ago 01:31
01:31
What is Digital Shadow?
What is a digital shadow, how does it appear, transform and what kind of life...
5 months ago 02:59
02:59
Tor Hidden Services
People need tools to ensure privacy. What are Tor Hidden Services and how can they...
2 months ago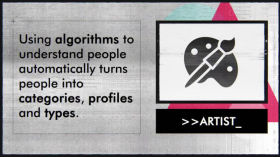 03:25
03:25
How to Create and Use Algorithms?
Using algorithms, you can reduce the time it takes to complete many tasks. However, you...
